Thank You
Our team will be in touch with you shortly.
In the meantime, here are some additional helpful links:
Online Resources
Additional Resources
Recent Articles

How to Secure Confidential Documents in a Hybrid Office Environment
When technology fails, business stops. That’s especially true when your confidential documents end up in the wrong hands. The hybrid workplace has rewritten the rules of document security, scattering your sensitive information across home offices, corporate locations, cloud platforms, and mobile devices. Each access point represents another potential vulnerability waiting
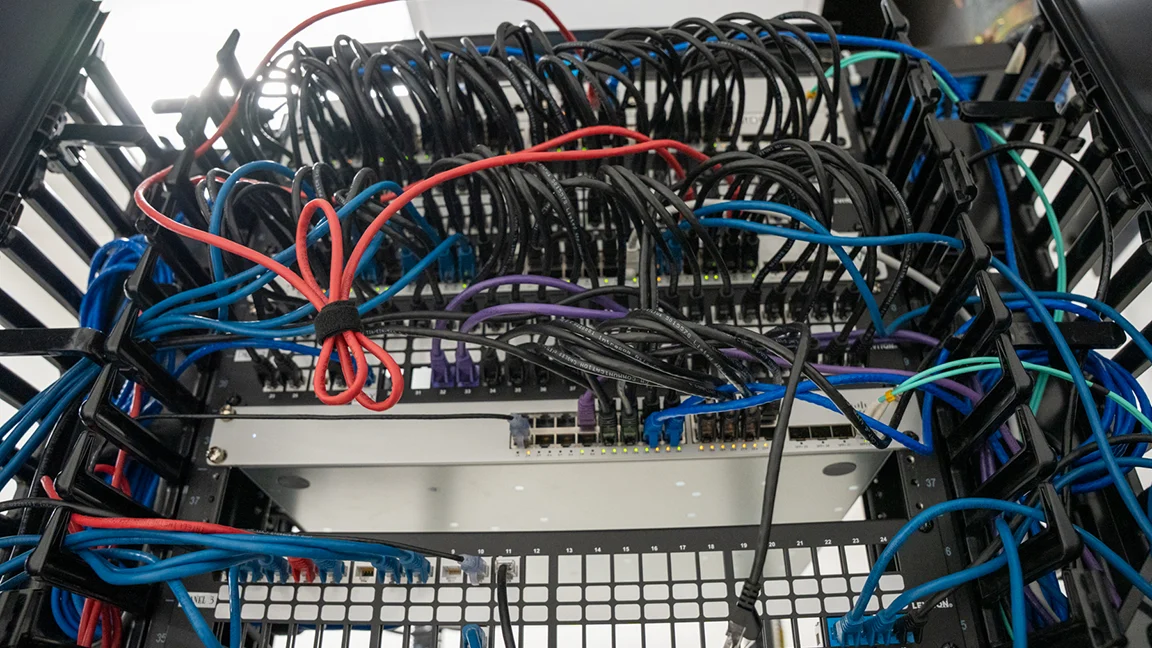
What are the Key Considerations for Network Monitoring and Management?
Network infrastructure operates as the circulatory system of modern business operations. Every transaction, communication, and data transfer depends on networks functioning reliably and securely. Yet many organizations approach network monitoring and management reactively, addressing issues only after they disrupt operations. Understanding what are the key considerations for network monitoring and

Staff Augmentation vs. Managed Services – Which is Right for Your Business?
Your business needs IT expertise, but the path forward isn’t always clear. Two dominant models compete for your attention and budget: staff augmentation and managed services. Each promises to solve your technology challenges, yet they operate from fundamentally different philosophies. The decision between staff augmentation vs managed services shapes more
