Thank You
Our team will be in touch with you shortly.
In the meantime, here are some additional helpful links:
Online Resources
Additional Resources
Recent Articles

What is Hard Drive Shredding?
Your business runs on data. Customer records, financial information, proprietary research, employee files—all stored on hard drives throughout your organization. But what happens when those drives reach the end of their useful life? Deleting files doesn’t actually erase them. Reformatting creates an illusion of security while leaving data vulnerable to

How to Secure Confidential Documents in a Hybrid Office Environment
When technology fails, business stops. That’s especially true when your confidential documents end up in the wrong hands. The hybrid workplace has rewritten the rules of document security, scattering your sensitive information across home offices, corporate locations, cloud platforms, and mobile devices. Each access point represents another potential vulnerability waiting
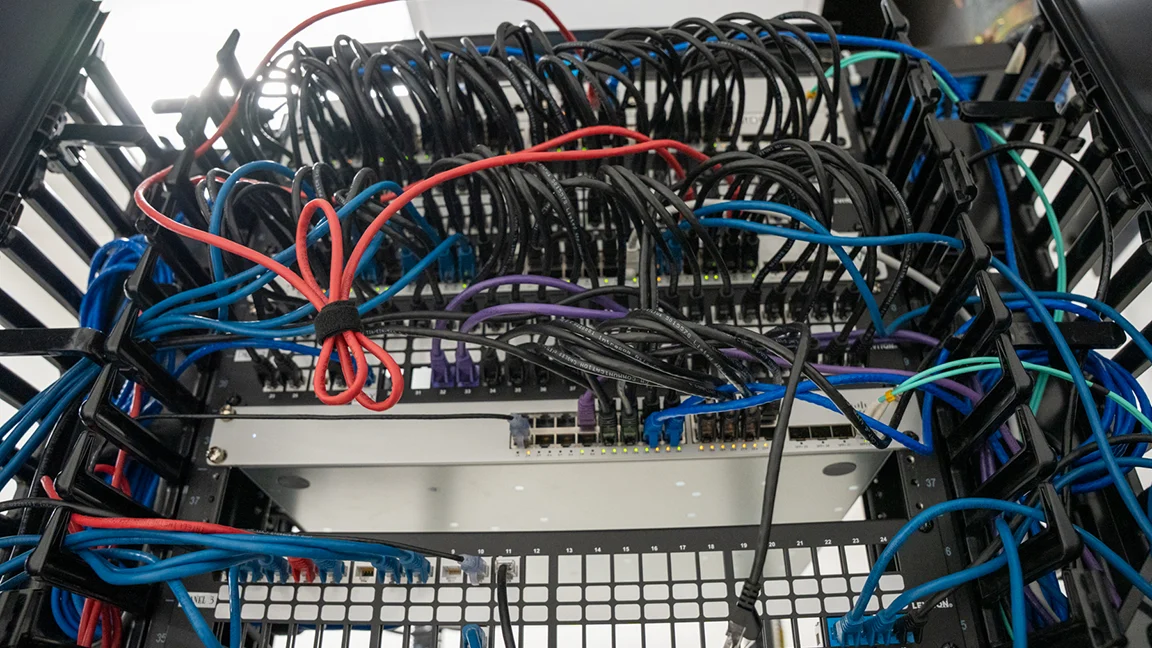
What are the Key Considerations for Network Monitoring and Management?
Network infrastructure operates as the circulatory system of modern business operations. Every transaction, communication, and data transfer depends on networks functioning reliably and securely. Yet many organizations approach network monitoring and management reactively, addressing issues only after they disrupt operations. Understanding what are the key considerations for network monitoring and
