
How to Secure Confidential Documents in a Hybrid Office Environment
When technology fails, business stops. That’s especially true when your confidential documents end up in the wrong hands. The hybrid workplace has rewritten the rules

When technology fails, business stops. That’s especially true when your confidential documents end up in the wrong hands. The hybrid workplace has rewritten the rules
Though RAID and back-ups can be both useful in protecting businesses from data loss, they are not the same thing nor can they be used
With newsfeeds being filled with headlines about data breaches, hacked networks and encrypted data held at ransom, its little wonder businesses are seeking ways to better secure their networks — and rightly so…
We’ve all seen the commercials featuring Mayhem, a bruised and battered Dean Winters in a disheveled grey suit, impersonating everything from a texting and driving teenage girl to a fiberglass-chewing…
Remote working, once thought mostly a nice idea, and perhaps largely only practiced in the tech sector, is now quite common thanks to Covid 19. In fact, according to one Forbes article, over the course of the pandemic, 45 percent of both…
It’s been said if you give a man a fish, you feed him for a day, but if teach him to fish, you feed him for a lifetime.
In a kind of a corollary to that, Bob Black, the founder of RK Black, is said to have told our copier technicians that…
Keeping your organization’s data secure and private should be a top priority. Why? Because data breaches are becoming increasingly common, destructive, sophisticated and expensive. According to Inc. magazine…
Anybody using computers or any networked devices these days would likely agree — passwords can be cumbersome. They’re annoying to generate, difficult to remember and often frustrating to populate. To make them worse, they are required seemingly…

These days associates are logging in and putting in their hours from the comfort of home, some due to the many touted benefits of working from home — less stress, lower costs, no commute, better coffee and so on — or more recently…
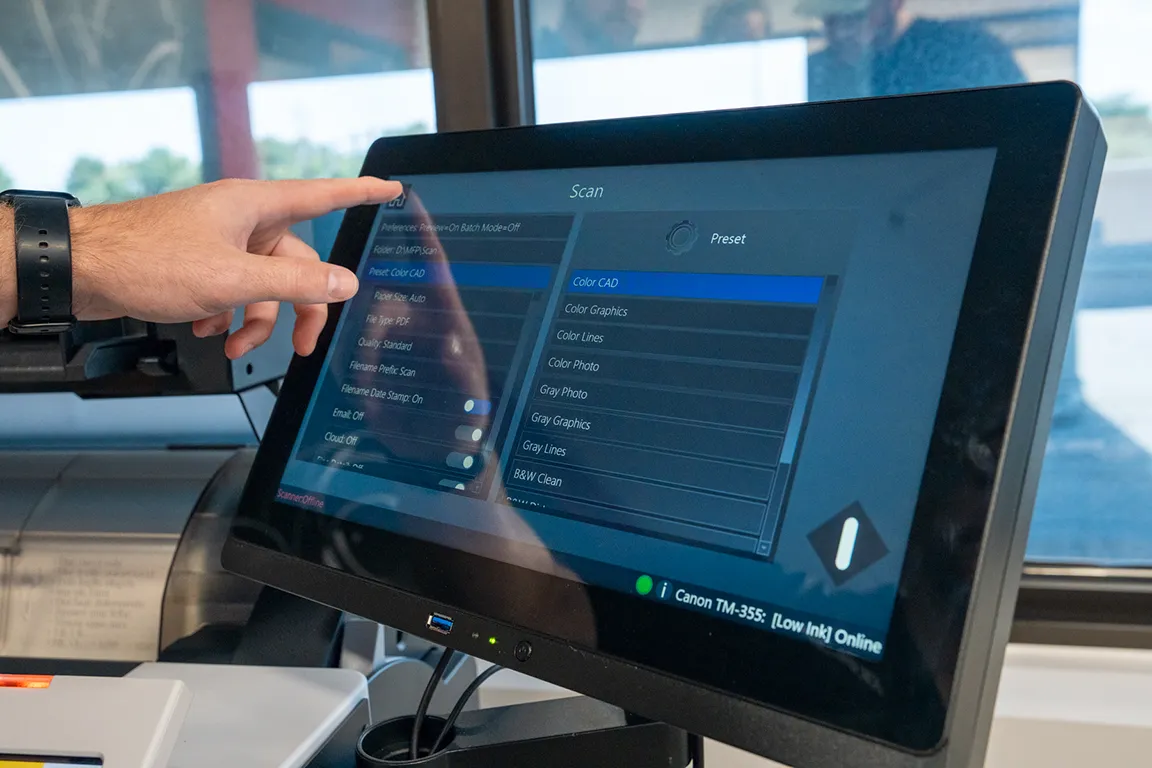
Right now, documents of all kinds are zipping across the world, from one computer to another, from one outbox to another inbox — some documents sensitive and some, not so sensitive.
With so many people now working remotely, many are using…

{ “@context”: “https://schema.org”, “@graph”: [ { “@type”: “Article”, “@id”: “https://www.rkblack.com/what-is-managed-it/#article”, “headline”: “What Is Managed IT? A Complete Guide to Services, Benefits, and What’s Included”, “description”: “What is managed IT? This complete guide covers what’s included in a managed IT agreement, how it compares to break/fix and in-house IT, pricing models,

Phone systems don’t get a lot of attention until they stop working. Then they get everyone’s attention at once. For businesses still running aging phone infrastructure — or cobbling together communication tools that were never designed to work together — the cost of inaction shows up in dropped calls, missed
Cybersecurity conversations have a way of generating more jargon than clarity. Two terms that appear constantly — microsegmentation and zero trust — are frequently treated as interchangeable, occasionally treated as competitors, and almost always underexplained. They’re neither the same thing nor mutually exclusive. Understanding the actual difference between them is

— Two things to fill in before deploying: 1. datePublished / dateModified — Fill in the actual publish date (ISO 8601 format, e.g., “2025-03-15”). This is required for Article rich results and Google News eligibility. If the page has no date visible to users, consider adding one — Google expects

Every business sends mail. Invoices, statements, compliance documents, marketing pieces — the volume adds up faster than most teams expect. For organizations still processing outgoing mail by hand, that volume also adds up in labor hours, postage mistakes, and delays that could have been avoided entirely. An automated mailing system
The copier salesman promises savings. The IT director warns about hidden costs. Your CFO wants data, not opinions. Managed print services generate this confusion because the value proposition isn’t immediately obvious. Unlike software subscriptions or equipment purchases, MPS transforms an entire business function most organizations have never properly measured. You

The question comes up during nearly every initial consultation: “How complicated is this going to be?” Business leaders considering a document management system want to know what they’re getting into before committing resources. The honest answer? It depends on factors most organizations don’t consider until they’re already knee-deep in implementation.

Your business runs on data. Customer records, financial information, proprietary research, employee files—all stored on hard drives throughout your organization. But what happens when those drives reach the end of their useful life? Deleting files doesn’t actually erase them. Reformatting creates an illusion of security while leaving data vulnerable to

When technology fails, business stops. That’s especially true when your confidential documents end up in the wrong hands. The hybrid workplace has rewritten the rules of document security, scattering your sensitive information across home offices, corporate locations, cloud platforms, and mobile devices. Each access point represents another potential vulnerability waiting