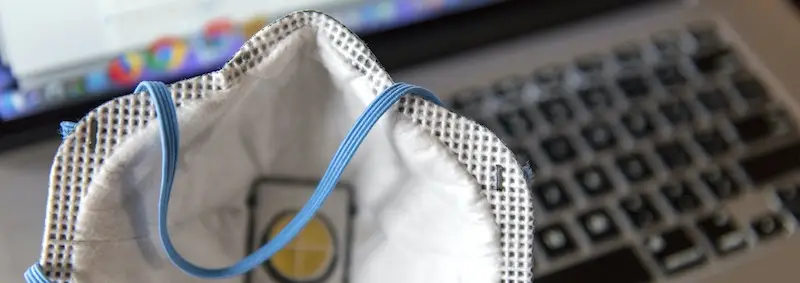
Beware: Coronavirus-related emails may be phishing attempts
Apparently the challenges today with businesses struggling for life and people fighting to make ends meet amid these Coronavirus-related shutdowns are just not enough. Bad actors are now trying to infect computers and networks with electronic…